What is a Business Email Compromise?
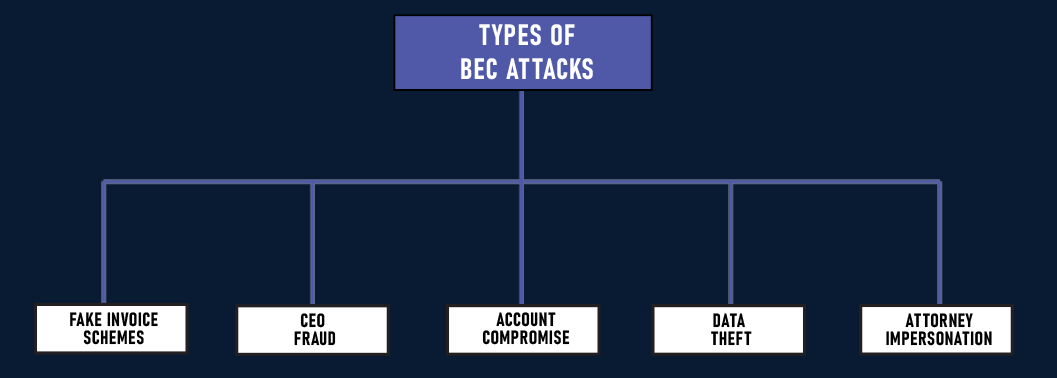
Business Email Compromise (BEC) is a sophisticated cyberattack that targets organizations by exploiting their use of email communications. It typically involves fraudulent schemes where attackers impersonate high-ranking executives or reliable business partners to deceive employees into transferring money or sensitive data. The attack often begins with phishing emails designed to gain credentials, facilitating unauthorized access to official email accounts.
Once control is established, attackers manipulate email conversations to redirect payments or request confidential information. BEC poses significant financial and data security risks, making vigilance and preventive measures such as employee training, email authentication protocols, and swift incident responses crucial for organizations to defend against this threat.
Example scenario with CyberGuard 6
A breach at Redacted INC exposed personal identifiable information (PII) of clients and compromised critical financial records. The data was used by the attacker for targeted fraudulent activities, presenting significant risks to the company and its partners.
To avoid detection, the attacker manipulated the email system by creating rules that redirected emails from partners to obscure folders, concealing legitimate communications. With the gathered information, counterfeit invoices branded with Redacted INC's logo were sent to clients and partners. These fake invoices contained fraudulent payment instructions, resulting in partners unknowingly processing payments into the attacker’s accounts.
Redacted INC's cybersecurity team, in collaboration with Cyberguard 6, executed a swift and thorough response strategy. This included securing the compromised account, using forensic methods to assess the breach's scope, and maintaining open communication with affected parties. Enhancing email security protocols was critical, and the team reviewed and strengthened authentication processes to prevent future incidents.